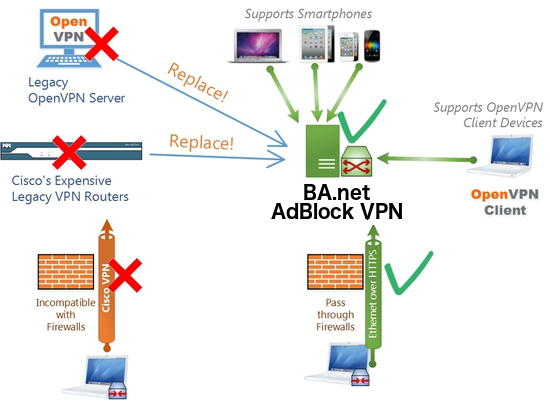
Business Turnkey Flashboot Server
Set up a Pi-Hole Ad Blocking VPN Server
Cloud-Hosted, Self-Hosted, Demo Live Service at
BA.net/adblockvpn
Debian Update & Upgrade
Once you log into your Linux machine or Virtual Machine via SSH, you want to
update and upgrade it.
Ensure you have elevated root privileges by running this command in the bash shell:
sudo su
Update and upgrade by running this command in the bash shell:
apt-get update && apt-get upgrade -y
Pi-Hole Installation
Pi-Hole is a DNS based adblocker.
Ensure you have elevated root privileges by running this command in the bash shell:
sudo su
Install Pi-Hole by running this command in the bash shell:
curl -sSL https://install.pi-hole.net | bash
You will flow into a series of prompts in a blue screen.
Choose OK or answer positively for all the prompts until the "Select Protocols" question
appears. IPv6 needs to be deselected as shown below:
Choose OK or answer positively for all the other prompts.
Set a strong password that you will remember for the Web Interface
pihole -a -p
Log into the web interface using the External IP that you noted down earlier at
http://your-external-ip/admin/settings.php?tab=dns
Click Settings, and navigate to DNS.
Set your Interface Listening Behavior to Listen on All Interfaces on this page:
Click the Save Button at the bottom of the page.
PiVPN Installation
PiVPN is an OpenVPN setup and configuration tool.
Ensure you have elevated root privileges by running this command in the bash shell:
sudo su
Install PiVPN by running this command in the bash shell:
curl -L https://install.pivpn.io | bash
You will flow into a series of prompts in a blue screen. All of the default values are
appropriate.
Choose OK or answer positively for all the prompts until you have to choose an upstream DNS
provider. The default answer is Google. Choose Custom and set an IP Address of 10.8.0.1
The default answer to reboot is No at the end of the installer. It is fine to say No, we have
a few more things to edit while we're logged in as root.
OpenVPN Configuration
Ensure you have elevated root privileges by running this command in the bash shell:
sudo su
Get into the openvpn directory by running this command in the bash shell:
cd /etc/openvpn
Server Configuration for VPN over UDP on Port 1194
Edit server.conf. I use nano to edit by running this command in the bash shell:
nano server.conf
Comment out the line which reads push "redirect-gateway def1" so it reads as follows:
# push "redirect-gateway def1"
The longer the keep-alive interval the longer it will take either end of the openvpn connection
to detect whether the connection is no longer alive. Because mobile devices often lose
connectivity and regain it, lower values are desirable.
Comment out keepalive 1800 3600 and add keepalive 10 60 below it, so it appears as follows:
# keepalive 1800 3600
keepalive 10 60
Comment out the line which reads cipher AES-256-CBC and add cipher AES-128-GCM below it, so it
reads as follows:
# cipher AES-256-CBC
cipher AES-128-GCM
At the bottom of the file add the following lines:
# performance stuff
fast-io
compress lz4-v2
push "compress lz4-v2"
Press CTRL O to bring up the save prompt at the bottom of Nano, press Enter to save. Then press
CTRL X to exit
Server Configuration for VPN over TCP on Port 443
Ensure you have elevated root privileges by running this command in the bash shell:
sudo su
Get into the openvpn directory by running this command in the bash shell:
cd /etc/openvpn
To accept incoming OpenVPN connections over TCP on port 443 we need a separate configuration
file. We can clone our existing configuration as a starting point, by running this command in
the bash shell:
cp server.conf server_tcp443.conf
Edit server_tcp443.conf. I use nano to edit by running this command in the bash shell:
nano server_tcp443.conf
Replace the proto udp and port 1194 lines with:
proto tcp
port 443
Edit the server 10.8.0.0 255.255.255.0 line to reflect an IP address of 10.9.0.0, so it reads
as follows:
server 10.9.0.0 255.255.255.0
Edit the push "dhcp-option DNS 10.8.0.1" line to reflect an IP address of 10.9.0.1, so it reads
as follows:
push "dhcp-option DNS 10.9.0.1"
Comment out keepalive 10 60 and add keepalive 10 120 below it, so it appears as follows:
# keepalive 10 60
keepalive 10 120
Comment out fast-io so it looks like this:
# fast-io
Press CTRL O to bring up the save prompt at the bottom of Nano, press Enter to save. Then press
CTRL X to exit
Add the OpenVPN service on Port 443 by running this command in your bash shell:
systemctl enable openvpn@server_tcp443.service
Finalize VPN Confgurations on Server
Reboot the server by running this command in your bash shell:
shutdown -r now
Managing the PiVPN
Connect to the Pi-Hole server and set up an OpenVPN Client Profile. (You do not need to have
elevated root privileges to do this.)
pivpn add nopass
Give your client profile a name. I like to use an alphanumeric string composed of the user's
first name, and their device's make and model (no spaces and no special characters).
NOTE
Make a new client profile for every device. DO NOT share a client profile between two different
devices.
This command will output a success message which looks like this:
========================================================
Done! banet-adblock.ovpn successfully created!
banet-adblock.ovpn was copied to:
/home/myusername/ovpns
for easy transfer. Please use this profile only on one
device and create additional profiles for other devices.
========================================================
To get the banet-adblock.ovpn file to your phone it is easiest to maximize your SSH window and
print the file to the terminal window, to copy & paste the output:
cat ~/ovpns/banet-adblock.ovpn
Press CTRL - until the screen zooms out to a point where you can see the entire ovpn file
printed on the screen. The first line will have the word client and the last line is .
Highlighting this entire chunk with a mouse will cause a scissor icon to appear in the middle of
your SSH window, this means this selection has been copied to your clipboard.
Saving a Split Tunnel VPN Client Profile for UDP VPN Connections on Port 1194
Paste this into your favorite Text Editor and save the file with a name that is clear:
banet-adblock-udp-1194-split-tunnel.ovpn
Around Line 12, edit the line which reads cipher AES-256-CBC and change it to read:
cipher AES-128-GCM
Saving a Full Tunnel VPN Client Profile for UDP VPN Connections on Port 1194
Copy the contents of banet-adblock-udp-1194-split-tunnel.ovpn and paste it into your favorite
Text Editor, save the file with a name that is clear: banet-adblock-udp-1194-full-tunnel.ovpn
Below cipher AES-128-GCM add this line:
redirect-gateway def1
Saving a Split Tunnel VPN Client Profile for TCP VPN Connections on Port 443
Copy the contents of banet-adblock-udp-1194-split-tunnel.ovpn and paste it into your favorite Text
Editor, save the file with a name that is clear: banet-adblock-tcp-443-split-tunnel.ovpn
Change proto udp on Line 3 to proto tcp
proto tcp
Change the 1194 at the end of Line 4 to 443, do not change the IP address on this line
remote YOUR-EXTERNAL-IP-IS-HERE-LEAVE-THIS-AS-IT-IS 443
Saving a Full Tunnel VPN Client Profile for TCP VPN Connections on Port 443
Copy the contents of banet-adblock-tcp-443-split-tunnel.ovpn and paste it into your favorite
Text Editor, save the file with a name that is clear: banet-adblock-tcp-443-full-tunnel.ovpn
Below cipher AES-128-GCM add this line:
redirect-gateway def1
Make these .ovpn files available on your phone or tablet.
E-mail these files to yourself
Client Config
Hardware Web Filtering VPN on your Local Network
(Self-Hosted)
Pendrive Software Appliance
![]()

![]() BA.net/adblockvpn
BA.net/adblockvpn
![]() .
.
![]() .
.
![]() .
.
![]() .
BA.net - AdBlock Split Speed VPN for Mobile iPhone iOS Android Save Data Usage
content filter tracking profiling openvpn blinkt tunnelblick pptp malware protection business security library campus school cybercafe cipa affordable easy alternative for legacy cisco vpn umbrella webtitan barracuda fortinet sonicwall sophos untangle managed pihole vpn adblock-speed-vpn-iphone adblock@ba.net
.
BA.net - AdBlock Split Speed VPN for Mobile iPhone iOS Android Save Data Usage
content filter tracking profiling openvpn blinkt tunnelblick pptp malware protection business security library campus school cybercafe cipa affordable easy alternative for legacy cisco vpn umbrella webtitan barracuda fortinet sonicwall sophos untangle managed pihole vpn adblock-speed-vpn-iphone adblock@ba.net